Mark Stenmark, MHSA, FACMPE
Senior Director, Insurance Services
Thanks to advances in technology, patients have access to more effective treatment options, caregivers have access to tools that allow for greater efficiency and researchers have access to data that helps fight disease. But, there’s a downside to all the access this technology provides. While organizations are aware of the need for improved security, the rise in health care data breaches in recent years is shocking. In fact, according to the HIPAA Journal, a staggering 13,236,569 medical records were compromised in 2018 alone.
A recent review of articles found on Beazley Academy, the educational arm of the global specialist insurer, focuses on the importance of keeping health care organizations and their associated business entities HIPAA compliant with regard to electronic protected health information (ePHI). As keepers of the public trust, they are counted on by patients, governmental agencies and business associates to implement strategies that preserve the safety of ePHI. To ensure that your organization is adequately protected against an information breach, consider the following recommendations.
First, every health care organization must meet the requirements outlined in the HIPAA Security Rule, which establishes standards that protect electronic personal health information. This includes knowledge of what ePHI is, where it is located, how and with whom it is shared, what constitutes a breach and what active measures should be taken to protect the organization against risks.
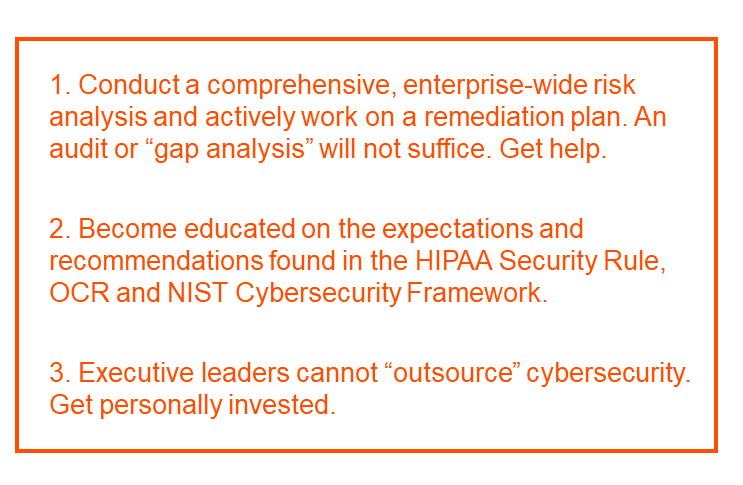
Second, conduct a comprehensive, enterprise-wide risk analysis that conforms to the Security Rule requirements. A risk “gap analysis” or audit is not sufficient. More than 80% of the Security Rule violations that end in a financial penalty or settlement are due to a lack of a comprehensive risk analysis. Because this is a heavy lift for most organizations, consider hiring an experienced, qualified consulting firm to assist you and your cybersecurity officer (CSO).
Third, the civil regulatory enforcement of HIPAA is conducted by the Office for Civil Rights (OCR), within the federal government’s Department of Health and Human Services. Every organization should pay careful attention to the monthly cybersecurity newsletter published by the OCR. In the event of a cyber breach, however malicious and damaging it may be to your organization, you will not be viewed as the victim. The patient is the victim and the OCR will investigate you as a potential violator of that trust.
There was speculation that the OCR might relax enforcement in accordance with reduced regulations seen in other sectors of government, but that didn’t happen. In 2018, the OCR levied a fine of $16 million to Anthem after a series of cyber breaches exposed the ePHI of nearly 79 million people. Among the list of violations? Failure to conduct an enterprise-wide risk analysis. Investigations are taking more time to conduct, averaging more than four years to complete. The average resolution settlement is $2.6 million.
Lastly, organizations are also encouraged to study the Cybersecurity Framework developed by the National Institute of Standards and Technology (NIST). Originally published in 2014 – and updated last year – the Framework helps organizations to better understand and improve their management of cybersecurity risk. Guidance is provided in common and accessible language, making it especially helpful in communicating inside and outside an organization. Considered a living document, the Framework will continue to be updated and improved as industry provides feedback on implementation. Your cybersecurity consultant and CSO will be able to help you implement a cyber defense program that follows the risk identification and stratification guidelines of this well-recognized framework.
In the inimitable words of educator, author and speaker, Stephen Covey, “The main thing is to keep the main thing the main thing.” In this case, the main thing is protecting your organization against an information breach. As health care leaders, I recommend that you become personally invested in the ever-changing landscape of cybersecurity. Every employee from the front desk to the boardroom has a role to play every day. There are many experienced and qualified resources available to help you and your CSO.
For more information about how Vizient can help support your organization’s efforts to create a more secure cyber environment, contact Mark at mark.stenmark@vizientinc.com.
About the author
Mark Stenmark serves as the national property and casualty (P&C) leader for Vizient Insurance Services. He is responsible for strategy, product development, sales, marketing, P&L, contract negotiations and the maintenance of multi-year B2B relationships with national insurance carriers and P&C broker partners. In his 23 years with the company, Stenmark also held regional and national positions in market management, business development, sales operations and purchased services